– What are the different types of cyber threats that can lead to cyberwar?
**Title: The Growing Threat of Cybersecurity and Cyberwar: Protecting Your Data in the Digital Age**
**Introduction:**
In today’s increasingly digital world, the threat of cyber attacks and cyberwarfare has become a major concern for individuals, businesses, and governments alike. With the rise of technology and interconnected networks, the risk of cyber threats looms large, making it more important than ever to prioritize cybersecurity measures to protect sensitive data and information.
**The Importance of Cybersecurity:**
Cybersecurity refers to the practice of protecting systems, networks, and data from digital attacks. These attacks can come in various forms, ranging from malware and phishing scams to sophisticated hacking attempts. The consequences of a successful cyber attack can be devastating, leading to data breaches, financial losses, and damage to a company’s reputation.
As technology continues to evolve, the methods and tactics used by cybercriminals are also becoming more advanced. It is crucial for individuals and organizations to stay vigilant and proactive in safeguarding their data against potential threats. Implementing robust cybersecurity measures is essential to mitigate risks and ensure the security of sensitive information.
**Cyberwarfare and National Security:**
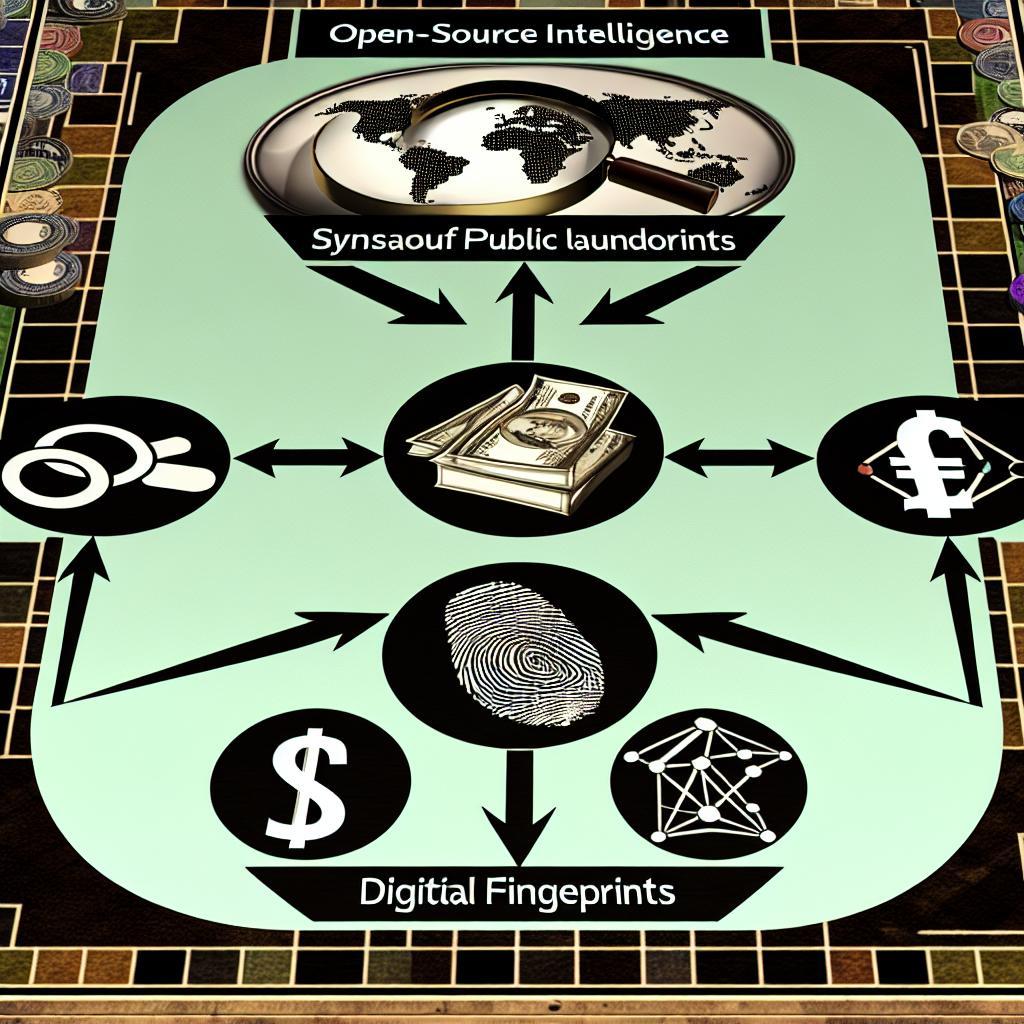
Cyberwarfare has emerged as a significant threat to national security, with state-sponsored cyber attacks becoming increasingly common. Countries around the world are investing heavily in cyber capabilities to engage in espionage, sabotage, and other malicious activities. These attacks can target critical infrastructure, government agencies, and military systems, posing a serious threat to national defense and stability.
In response to the growing threat of cyberwarfare, governments are ramping up their cybersecurity efforts to defend against potential attacks. Collaboration between public and private sectors is crucial in developing robust defense strategies and sharing threat intelligence to prevent cyber incidents.
**Benefits of Cybersecurity Measures:**
– Protecting sensitive data: Implementing strong security measures can help safeguard personal and business data from unauthorized access.
– Preventing financial losses: Cyber attacks can result in significant financial losses, making cybersecurity investments a cost-effective measure to mitigate risks.
– Maintaining customer trust: By demonstrating a commitment to cybersecurity, businesses can build trust with customers and protect their reputation in the marketplace.
**Practical Tips for Improving Cybersecurity:**
– Use strong, unique passwords for all accounts
– Enable two-factor authentication for added security
– Keep software and systems updated regularly to patch vulnerabilities
– Educate employees on safe cybersecurity practices
– Implement firewalls and encryption to protect networks and data
**Case Studies:**
**Company X**: By strengthening their cybersecurity measures and conducting regular security audits, Company X was able to prevent a potential data breach and protect customer information from unauthorized access.
**Government Agency Y**: Government Agency Y collaborated with cybersecurity experts to analyze and mitigate potential threats, enhancing their defense capabilities against cyber attacks and safeguarding critical government systems.
**Conclusion:**
As the threat of cyber attacks and cyberwarfare continues to escalate, prioritizing cybersecurity measures is essential to protect data and information in the digital age. By investing in robust security protocols, staying informed about emerging threats, and fostering collaboration between stakeholders, individuals, businesses, and governments can enhance their defense against potential cyber threats. Remember, cybersecurity is everyone’s responsibility in safeguarding the digital landscape for a secure and resilient future.
In conclusion, cybersecurity and cyberwarfare are complex and evolving challenges that require continuous vigilance and proactive measures to mitigate risks effectively. By staying informed, implementing best practices, and fostering collaboration, individuals, businesses, and governments can enhance their cybersecurity defenses and protect sensitive data in the digital age.